Business logic flaw in the invitation system allows to Takeover any account at a private company
Hello Friends,
In this post, I’ll explain how I could exploit a business logic flaws under the invitation system from a private company to take over any account in their services without user’s consent.
First things first:
I have a team named “Vendetta” and there was a new target that launched a public bug bounty program that we found trough google dork, so we decided to take the first “critical” look
Normally I start to use the application as a normal user while I capture and read ALL requests using a traffic interceptor tool (e.g. Burp Suite).
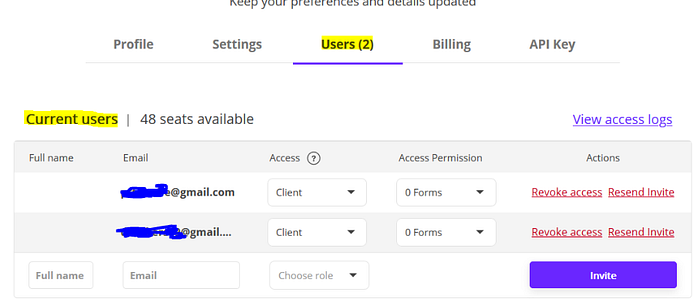
The application allowed us to invite new users to the organization account under “Users” section
The invited user will then receive an email in their mail box with a token as below
https://app.redacted.com/reset-multi-user-password/INVITE-TOKEN-HERE
If you are a Bug hunter then the above endpoint should get your attention as it drew mine, especially in reset-multi-user-password
As I explained, the function was created to add a user to the company’s account, why are they calling this “reset password” endpoint?
With this question in mind, I decided to go deeper, when accepting the invitation , the application sent a POST request to the endpoint/activate-invited-user along with the invited email in the request body.

The problem lies here, where the invited user has control over the email and password in the request body, I thought:
“The invited user receives the invite token by thereset-multi-user-password endpoint, the user controls the invited email and new password, what If I change the invited email to owner@victim.com and forward the request along with a new password?”
Finally, I captured the “accept invite” request and change the email to “owner@victim.com” along with a new password as follows
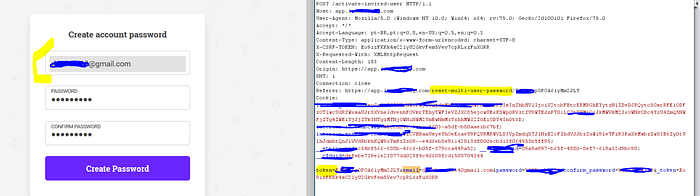
And the server accepted my request, next I logged in as “owner@victim.com” with the new password to confirm the takeover.
Finally, I sent an email describing the vulnerability and the impact with below Proof of Concept to the security team:
- Login to your account at https://app.redacted.com
- Now invite any email that you also control under “Users” section
- Click in the invite link and you’ll see a page where it will ask for you to create a new password for the account, intercept the request
- Just change the
emailto any other user account at your application and forward the request - You have now set a new password for the “victim” email using an invitation token
The security team quickly triaged and resolved this vulnerability.
Takeaways:
Always observe all the endpoint names, if you see something different than the usual, try to go deeper, you may find some interesting behaviours with them.
Thanks for your time :)
Daniel_v
Vendetta White hat Team

