How I hacked a news website?
Hey guys, It’s me Krishnadev P Melevila Again!! I am a self-made cyber enthusiast and Web application pentester.
Here, now I am writing about a local news website, I came to know about this site through an Instagram story of a social media influencer, I saw that his article was posted on that site so suddenly from somewhere a thought came to my mind! — Let’s hack and add my article by myself on the site.
So I just opened the site and check for the vulnerabilities, As soon as I checked, I found a login page. But I was 100% sure that it was not an admin login panel and it is just a frontend login.
But that frontend login was SQL Injection vulnerable and I just opened the burp suite and copied that POST request and exploited it in sqlmap. Yahoo!! I got the complete database.
But all the passwords are hashed! I don't like decrypting hashes!
But wait!!!! I found an interesting matter. Many of the hashes on there are the same. That means, there are two possibilities, 1. All the user credentials are created by the same person using some same passwords 2. There are some common passwords so more than one user using the same password
So it will be easier for me now. I just opened an online MD5 Decryptor and entered one of the hashes. Within seconds, I got the decrypted password as 12345
VICTORY!!!
Now the problem is, I don't know the admin panel URL. No worries Just opened the robots.txt and there it is...
Quickly went to admin panel and entered the creds as user-admin and pass-12345
Yeah!! now I am on the news admin panel!!!!
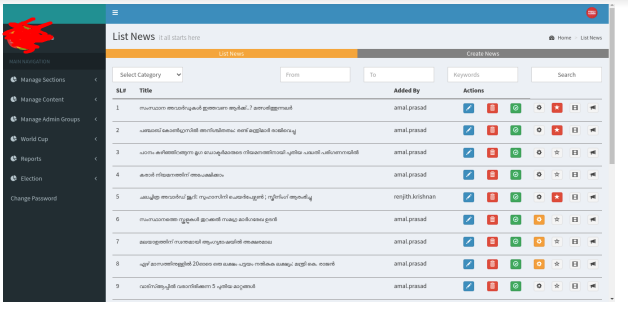
But it not ends here! I came to know about the image upload feature on the news portal. Yes, just check the Remote Code Execution! I tried uploading a shell on the server and it uploaded successfully without any validations.
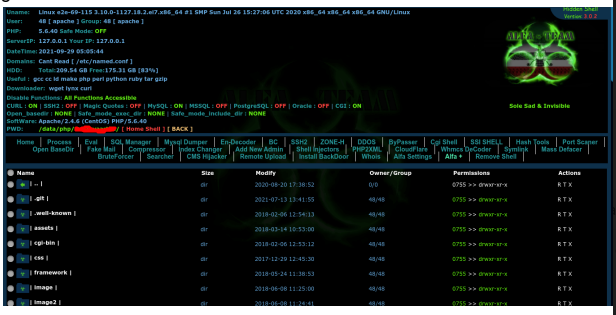
And here we got complete access to the server. Now I can able to destroy the complete website. But, as a concerned cyber security enthusiast, I always prefer to stay inside the ethics boundary so I reported all the incident and vulnerability to the site admin and they validated the report and patched it within 2 days.
My Instagram handle: https://instagram.com/krishnadev_p_melevila
My Twitter handle: https://twitter.com/Krishnadev_P_M
My LinkedIn handle: https://www.linkedin.com/in/krishnadevpmelevila/
My cybersecurity course selling website: https://learn.nodeista.com/
My Personnel website: http://krishnadevpmelevila.com/

