How I was able to find and exploit the Google Maps API key of a target and you can do it too
Hey, What’s Up Fellow Hackers & pro bug bounty hunters hope you are doing well and staying safe, hunting heavily and bunking online classes( Everyone Does xD). So today I am going to share an interesting story about one of my interesting finding in a program. I won't disclose this for obvious reasons so let’s assume it as redacted.com. So Are You Ready? If not grab a mug of coffee and then let’s begin
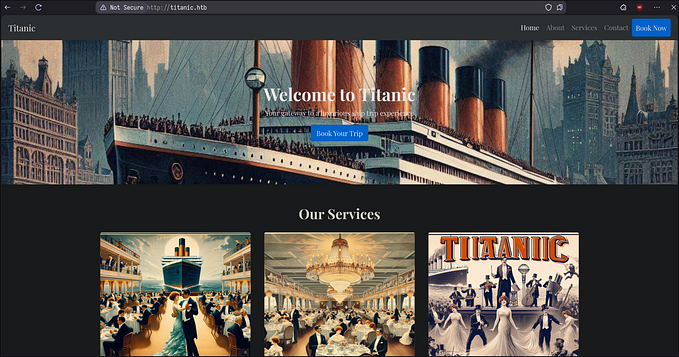
So it was just a normal day as we all spend in this pandemic, I chose a target and enumerated all its subdomains with the help of Subfnder and probed them using httprobe . Now I was visiting each and every subdomain from the list of all live subdomains and I suggest you the same, Don’t depend on the tools. Spent almost 3+ Hours found nothing juicy, almost all of them were static web pages. Took Some break, again continued and then a subdomain caught my eye. Because it was an Admin Login Page.
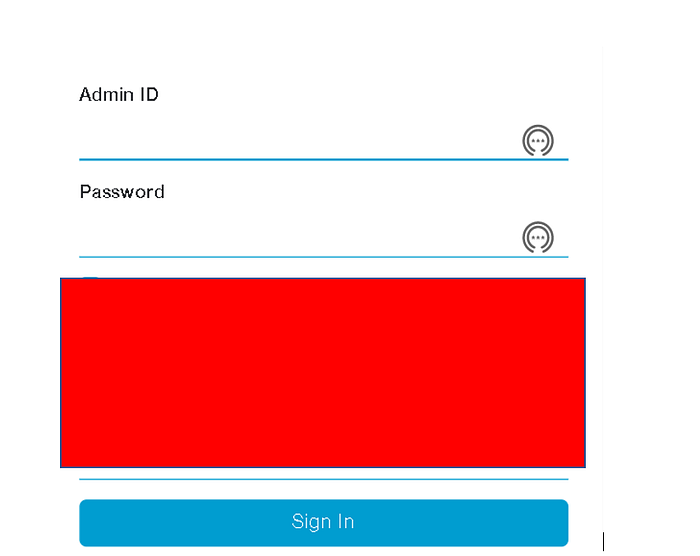
But nothing new. At first, I was also excited and tried everything that everyone does ( default credentials, enumeration, SQLi, and stuff) but not successful. I thought to give up after my final attempt of Google Dorking. But When Trying To Copy URL for dorking, by mistake I pressed CTRL+U instead of CTRL+C, and then the source code loaded and I saw something which made me happy and shocked.
Yeah Yeah! you guessed it right, it was the Google Maps API key being leaked in the source code ( often found in source code ). I was very happy because I almost thought to give up but suddenly my typing mistake got me something.
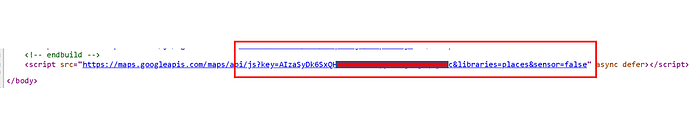
Then Quickly I rushed to the Keyhacks Github Repo ( Very Useful ) and then chose Google Maps API Key and copied the static map URL endpoint and copied my key and pasted it there. But what happened was not what I expected and I got sad. The Key was restricted
Back then I was a beginner so I didn’t know that we need to test the key in all endpoints because it may not be restricted for all endpoints so I did some research and came to knew about that and tried the key on all endpoints like Street View, Embed, Geocoding, directions and all the endpoints available in that Repo. And Fortunately, except Static Map Endpoint all the endpoints were vulnerable :)
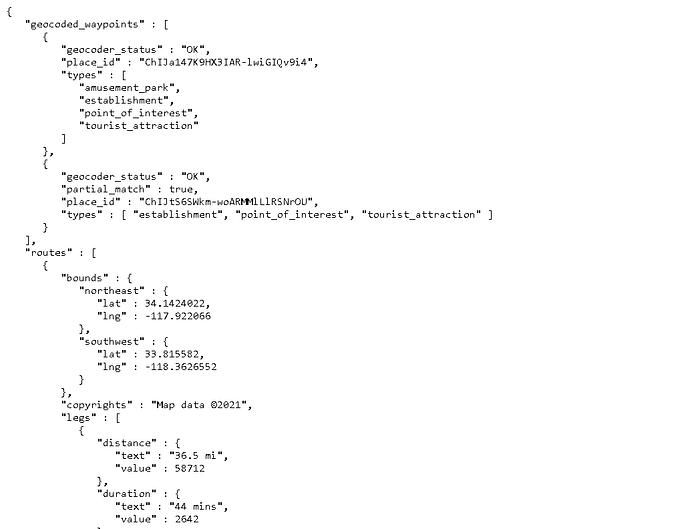
Which means now I was able to make unauthorized calls with the help of the API key which costs some good bill to the company. You can refer to the exact amounts on that repo. Also as an attacker, I was able to consume the Quota of the company if not configured or restricted and cause a Dos Attack if billing services were not configured properly. This means in short a huge Financial Damage to the company. Quickly made a Report with the POC and the only next day it was accepted and I was added to the Hall of Fame.
Takeaways
Check Each and every subdomain manually, look for sensitive endpoints in JS Files and source code you will find something juicy and also avoid using tools every time because remember “ Automation can’t Replace Manual Findings because it depends on the way you think and abuses the functionalities”
P.S: Bugcrowd mostly will not accept this submission or probably close this as an informative. I have heard this from lots of people but no one knows the reason. So better you should not waste your time finding this in Bugcrowd Programs. If you are hunting elsewhere like Hackerone, Intigrity and RDP’s, I am sure this will be accepted if not a duplicate.
So that was all about today, I hope you got some useful knowledge. If yes don’t forget to Give a Clap and connect with me on Twitter ( Dm’s are Always Open).
Signing Off!!! Peace
References
https://blog.dixitaditya.com/bypassing-google-maps-api-key-restrictions/