Member-only story
PicoCTF 2021: Transformation
The basic reverse engineering concept of a file hidden message.
The Back Story
I have been doing Bug Bounty for a couple of years now, as you may know, most of the people working in this field tend to share many similarities. The type of movies they watch, programs to work with, and even the same group of YouTubers to get information and learn more skills from.
But the thing most or just all Bug Hunters have in common are CTFs. I kind of knew what was it but never had a real interest in it just until today. Yes, today was my first time playing CTF. Somehow Youtube sent my way a video of a DEFCON conference talking about picoctf.org. At first, it wasn’t hard to find most flags until I scramble into “Transformation”
What is Capture The Flag?
Capture The Flags, or CTFs is a kind of computer security competition. Teams of competitors (or just individuals) are pitted against each other in a test of computer security skills. Very often CTFs are the beginning of one’s cybersecurity career due to their team-building nature and competitive aspect.

As we can see from the photo I was given a file to download, some python snippet code, and a hint to try to solve the flag. If you know your way around Python, this was the point to start from. Being me that’s not where I started, although I should have.
Let’s Get To The Action
First Shot
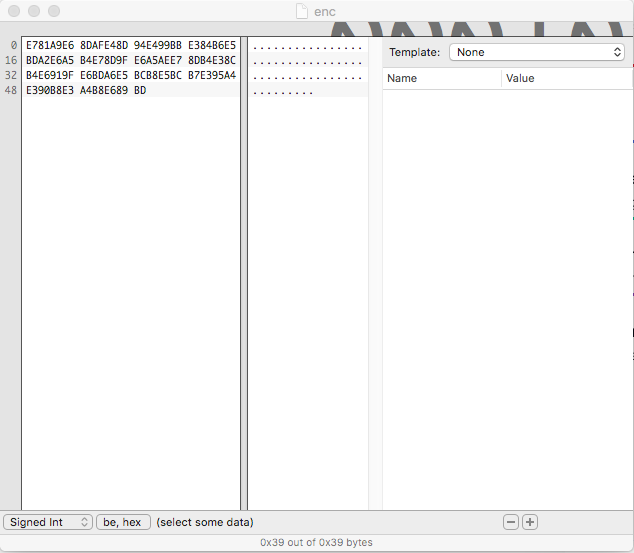
After downloading the file to a local directory for data analysis, I went ahead and toss it into a hex editor to check for any hidden secrets.