Privilege Escalation to Super Admin 💪
Intro:
Hey hackers!!! Hope u all are doing very well in you life. Today I will be sharing about a Privilege Escalation vulnerability I found on a client’s website.
I found a Privilege Escalation bug with IDOR which was leading me to gain super admin access. The website was not validating the user input in the request body.
Now lets move on to or main story.
Story of the Bug:
I was asked to test a client’s webapp, during my internship period. It was a good opportunity for me to test my skills and probably gain something valuable throughout my testing phase.
It was some kind of a user management app or something like that. There was invite fulctionality with different roles like Administrator, Marketer, Marketing Executive and bla bla bla….
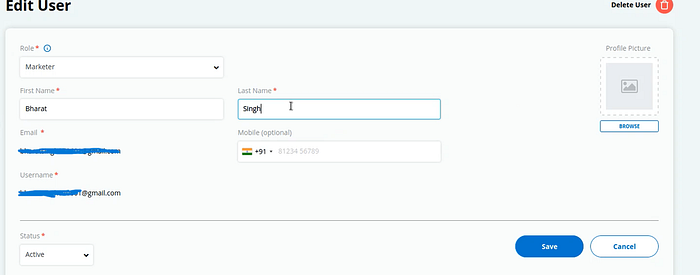
I created an Administrator account and send an invite to myself on my second email address with Marketer role priveleges. I accepted the invite in other browser’s window and started surfing on the administrator window to find something intresting.
I observed that only the Administrator can change the user role and other profile details.
When I went to edit profile option of the invited user I observed the request to be intresting. It was a POST request like this:
POST /user-management/update/123
I thought to play with this “123” three digit user ID to change other’s user profile data, but the response showed me error and I was unsuccessfull.
I went again to user profile edit option.
Clicked on save button and Intercepted the request in Burp.

Now this time I decided to manipulate the “role_id” parameter in the request body to value “1”.
I was expecting that it will promote the invited user to a Administrator.
I opened the Invited user’s browser window (Marketer) and refreshes the page and guess what, I am a Super Admin now.
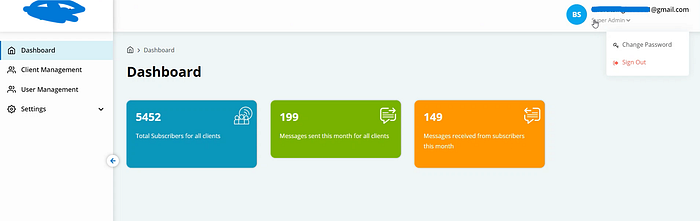
Invited user dashboard completly changes to the Super Admin Dashboard.
Now I have the complete control over the webapp.
Impact:
An attacker can gain the Super Admin access. This means that the attacker can access, modify, or delete any data in the application, including user information and sensitive data. Overall the Attacker can takeovers the whole website.
End:
I hope u guys have learned something valuable and enjoyed my writeup.
Show some love, by hitting that god damn 👏X50 times…
Feel free to connect with me on Linkedin and Twitter.

