Reflected XSS on Microsoft.com via Angular Js template injection
I got lots of message for Microsoft POC on Instagram and whatsapp also So i think write a blog for it.
Summary:-
Client-side template injection vulnerabilities arise when applications using a client-side template framework dynamically embed user input in web pages. When a web page is rendered, the framework will scan the page for template expressions, and execute any that it encounters. An attacker can exploit this by supplying a malicious template expression that launches a cross-site scripting (XSS) attack. As with normal cross-site scripting, the attacker-supplied code can perform a wide variety of actions, such as stealing the victim’s session token or login credentials, performing arbitrary actions on the victim’s behalf, and logging their keystrokes.
Browser cross-site scripting filters are typically unable to detect or prevent client-side template injection attacks.
I started my hunting on Microsoft from finding subdomains
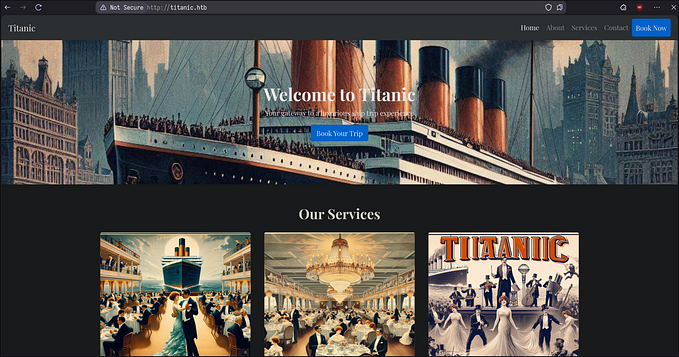
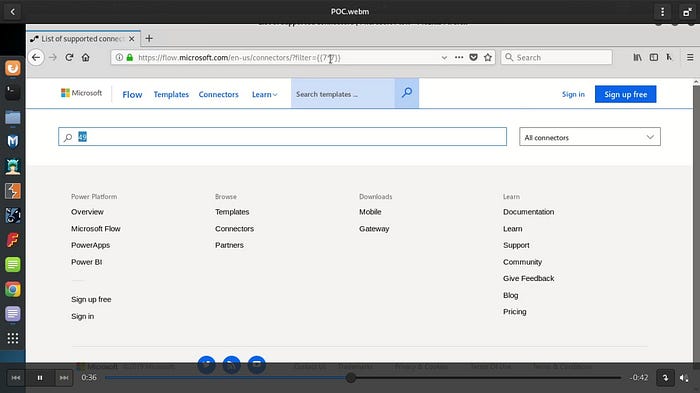
I got my target site which is https://flow.microsoft.com/ with some advance recon also Here i noted some points like which technology used by that websites
Angular templates can contain expressions — JavaScript-like code snippets inside double curly braces. To see how they work have a look at the following jsfiddle:
The text input {{7*7}} is evaluated by Angular, which then displays the output: 49.
This means anyone able to inject double curly braces can execute Angular expressions.
then start sort out the parameters and find out which is “filter”
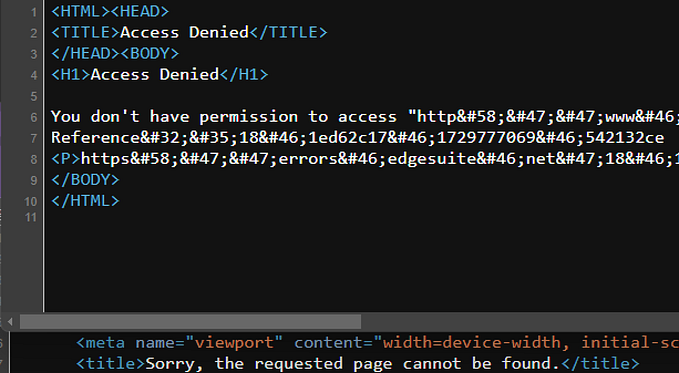
i used xss payload but no payload is working here :(
Then i manually checked where it values reflected in sources code then i realize that its by recon and source code reading that it is use a angular template and found a version of that template and search a payload for that here i got that payload
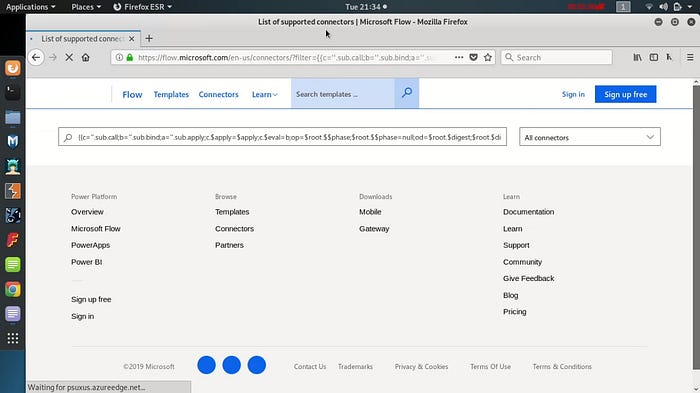
then i use Google for it and
https://portswigger.net/research/xss-without-html-client-side-template-injection-with-angularjs

Video poc:-
And Finally, I got Microsoft Hall of Fame.
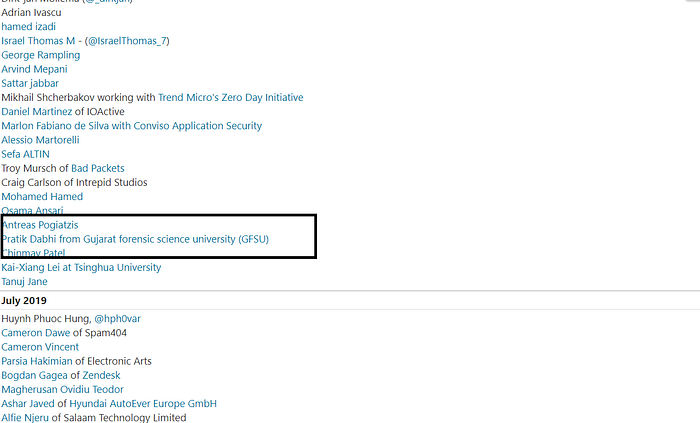
Timeline :
- 13-July-2019 — Report
- 18-July-2019 — Triaged
- 28-July-2019 — Valid & Fixed
- 20-August-2019 — Hall Of Fame
Thanks, everyone for reading:)
Happy Hacking ;)
Support me if you like my work! Buy me a coffee and Follow me on twitter.
Website:- https://www.pratikdabhi.com/
Instagram:- https://www.instagram.com/i.m.pratikdabhi
Twitter:- https://twitter.com/impratikdabhi
Youtube:- https://www.youtube.com/impratikdabhi