Member-only story
Simplifying Linux File Permissions
Changing Permissions with “chmod”: A Step-by-Step Guide
In this guide, we will explain how to set file permissions in Linux using various commands and techniques. Whether you’re a beginner or an experienced user, our step-by-step instructions will help you manage file permissions effectively.

There’s a lot of information in those lines.
The first character = _ or d or l
_ ➜ It’s a file
d ➜ It’s a directory
l ➜ The file or directory is a Symbolic link
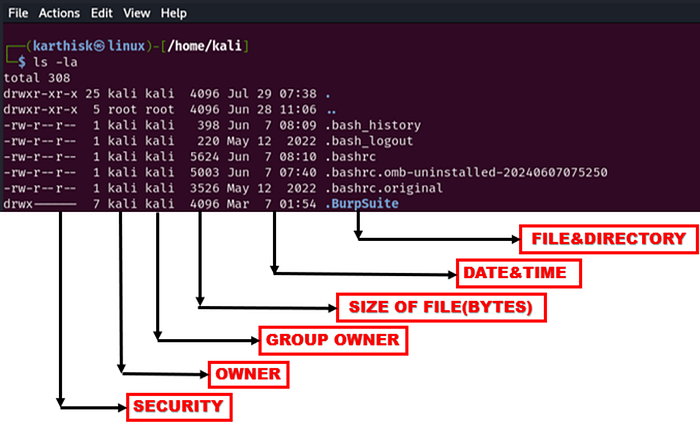
1. The next nine characters = (rw-r–r–) show the security
2. The next column shows the owner of the file. (Here it is `root`)
3. The next column shows the group owner of the file. (Here it is `root` which has special access to these files)
4. The next column shows the size of the file in bytes.
5. The next column shows the date and time the file was last modified.
6. Last Column = File_name or Directory_name. (For example, here are: prac, snap, test, example)
What are the three permission groups in Linux?
First, you must think of those nine characters as three sets of three characters (see the box at the bottom). Each of the three “rwx” characters refers to a different operation you can perform on the file.
--- --- ---
rwx rwx rwx
user group other1.Owners: These permissions apply exclusively to the individuals who own the files or directories.
The user permissions apply only to the owner of the file or directory, they will not impact the actions of other users.
2. Groups: Permissions can be assigned to a specific group of users, impacting only those within that particular group.