Testing and Bypassing Technique for IDOR
Insecure Direct Object reference

Hey Guys welcome to the blog today we are going to discuss one of the easiest vulnerabilities to understand which is IDOR and It has a high/critical impact on bug bounty So in this article we going to discuss Testing for IDOR and some bypassing techniques for IDOR finale we end up with portswigger lab
What is IDOR?
IDOR is nothing but insecure direct object reference it is one of the access control vulnerabilities
This happens when they give direct access to the resource which the users cannot able to access that resource without any validation
When an application fails to properly validate and authorize user access to specific objects or resources, it creates an opportunity for unauthorized users to manipulate or access sensitive information. This can happen when the application relies on insecure or easily guessable object identifiers, allowing attackers to bypass the intended access restrictions. IDOR vulnerabilities highlight the importance of robust access controls and thorough validation to protect against unauthorized access and maintain data privacy and integrity.
Two Types of IDOR
- Read-Based IDOR: Using this you can able to read that information not able to alter that data
- Write-Based IDOR: Using this you can able to read and write that information and it is a critical vulnerability
Testing for IDOR
Before going to testing keep in mind IDOR is not only on the profile page where every ID or sensitive data are there possible places
And first don’t test it keep notes where every area is possible which will avoid demotivation (Recon the endpoints)
- Create Two accounts on the same targets ( If you see some different privileges like group admin, users means to create multiple accounts, and if it is not possible ask the company to give the multiple accounts for testing )
- Now choose one is the Vitcim account and One is Attacker Account
- Check for functionality where the user can delete, create or change the password
- Check for any guessable ID in a private message or any other functionality
- Capture the request and analysis in the burpsuite
- API like REST ( Representation state transfer ) and GraphQL is most vulnerable to IDOR
- Change the ID if it returns any other resource it is vulnerable to IDOR
- Sometimes we need to change the HTTP Method POST to GET and POST to DELETE
Note: Pay Attention to the premium function because most of the testers and hackers won’t go for there due to some laziness or not paid
So Now Let’s move to Portswigger Lab
Lab: Insecure direct object references
This lab stores user chat logs directly on the server’s file system and retrieves them using static URLs. Solve the lab by finding the password for the user carlos, and logging into their account.
In this Lab, there is Live chat functionality using this we need to get Carlos password to solve the lab
So first go for Live chat functionality
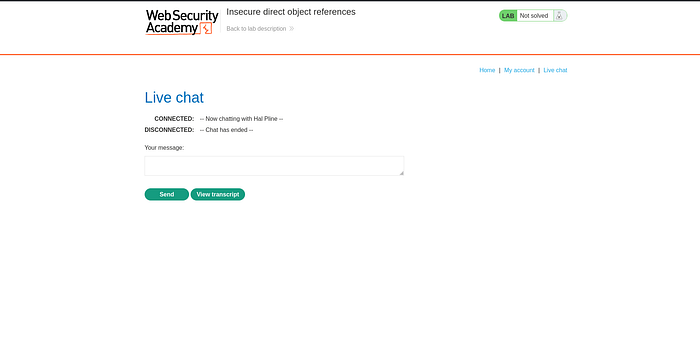
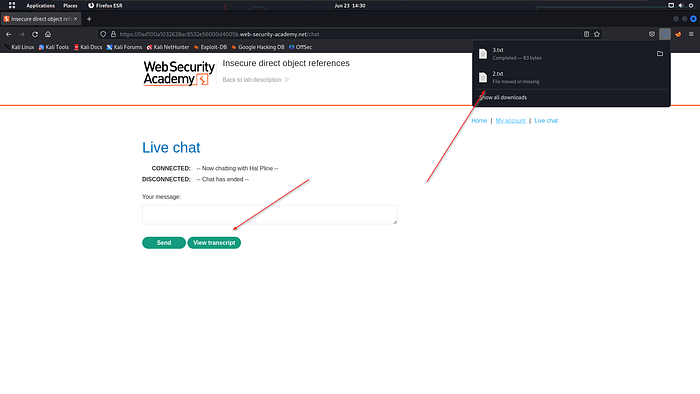
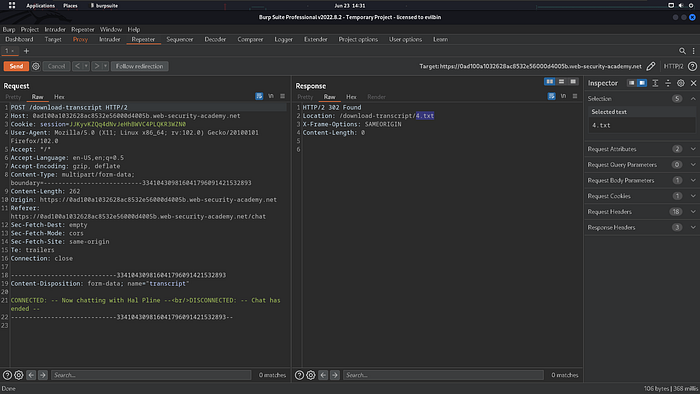
Here you can able to see the view transcript button using this you can able to download that transcript but it sends the transcript from the 2.txt, 3.txt, and 4.txt
In this case, you cannot able to get the 1.txt so think that the password is stored in the 1.txt
So Let’s get the 1.txt using the GET HTTP Method
First, capture the request
And change the method to the GET method as I said in STEP 8 ( in testing )
Add the /download-transcript/1.txt to view the file
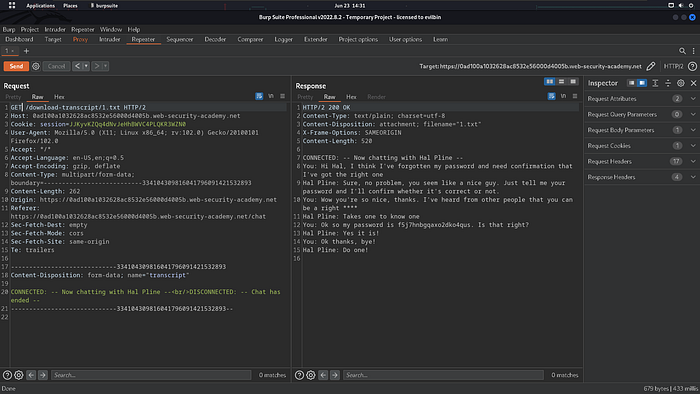
Boooooooooommmm!!! Now you will get the password
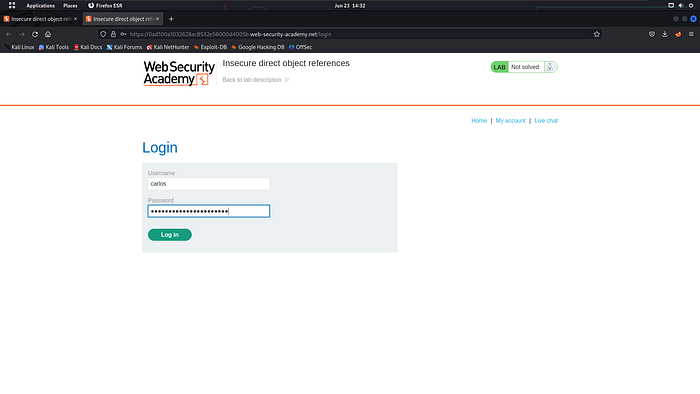
So login with username and password
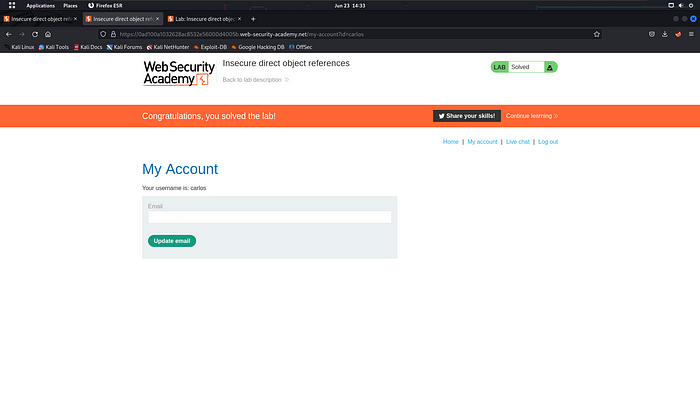
The Lab gets solved
From Lab Summary:
So Now you get a good idea about IDOR and important point check at every place the POST Method (sensitive place)
Nowadays IDOR became easy so everyone will find get patched it is hard to get the IDOR with a complex numeric ID so don’t worry there is a bypass technique to Bypass this protection
The strength of a system lies not only in its features but also in its ability to protect against Insecure Direct Object Reference vulnerabilities.
Leaked ID in Profile/Private Message
You can able to find the leaked ID in a private message or at the anywhere public profile
Using that ID we can able to retrieve the information
And you can be able to find this at Waybackurls sometimes
GET /messages?conversation_id=849849899938664746276776762767462474274
GET /messages?user_id=2763Blind IDOR
Blind IDOR happens at the monthly bill details or the endpoints do not respond to the leaked information directly and immediately
A subscription-based system like month receiving the details via email on that request changing ID send a request via you Mail can lead to the IDOR
Changing the Request Method
Changing the request method to GET, POST, PUT, DELETE, and PATCH because the developer implements the access control for GET and POST but failed to implement it for PUT, DELETE, and PATCH
Change the GET to DELETE
DELETE example.com/uploads/user1236-01.jpegChange the POST To GET
GET /get_receipt?receipt_id=2983Sometimes you can use the PUT to create Sometimes on another account
Chaining the bug with other
You can able to chain that bug with self xss and RCE (Remote code execution)
Automate of IDOR
https://github.com/Quitten/Autorize/
https://github.com/nccgroup/AutoRepeater
/https://github.com/SecurityInnovation/AuthMatrix/
I hope you will understand this if you feel this a helpful please give applause to this article and follow up on my profile for more updates
Donate to Me: https://buymeacoffee.com/0xevilox